Google OIDC Configuration
Pro only
Configuration at Google
-
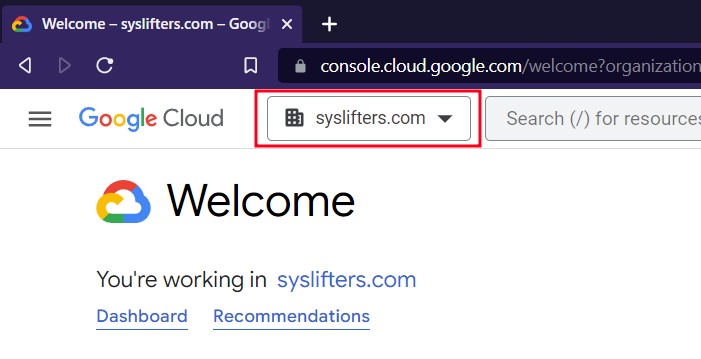
Open Google Cloud Console
- Make sure to select the correct organization:
-
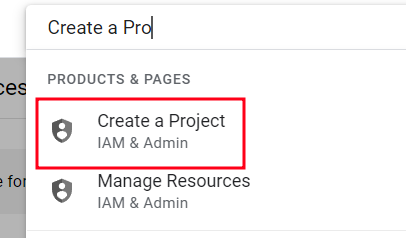
Use search box and click "Create a Project"
-
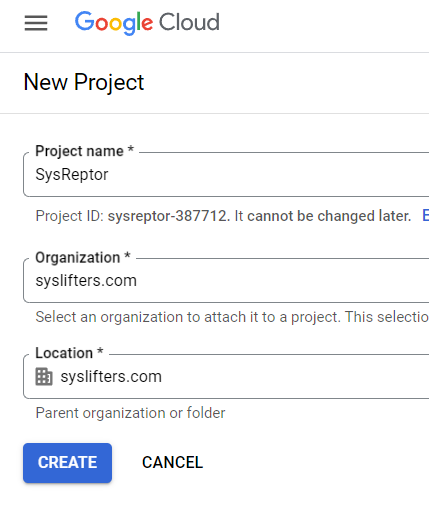
Enter Name, Organization, Location and "Create"
-
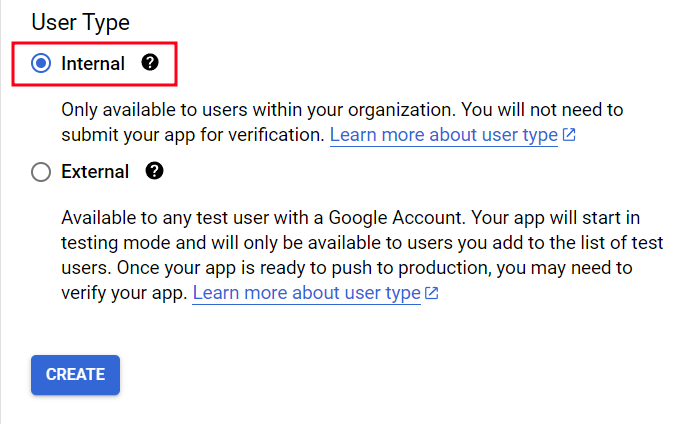
Search for and call "OAuth consent screen"
-
Select "Internal" for "User Type" and "Create"
-
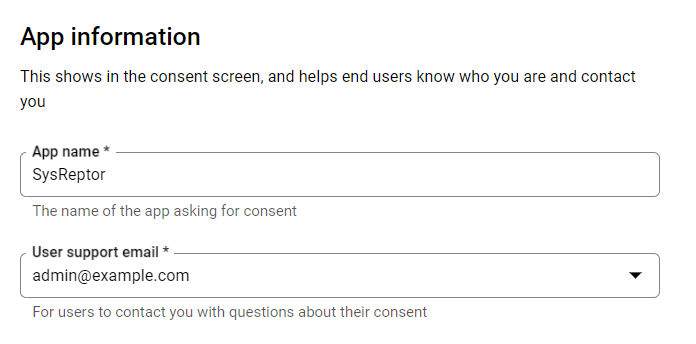
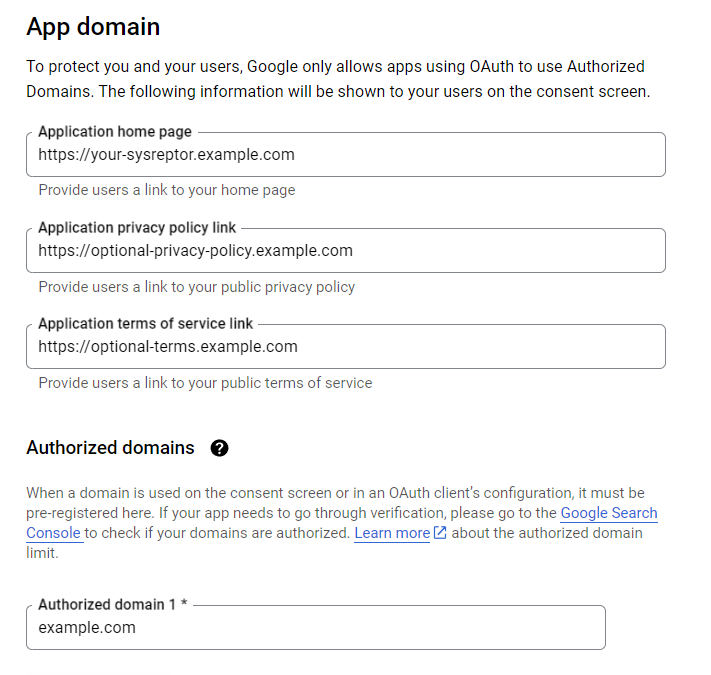
Enter "App information"
-
Optional: Add App logo
- You can use this
-
Enter App domain info
-
Enter Developer contact information and click "Save and Continue"
-
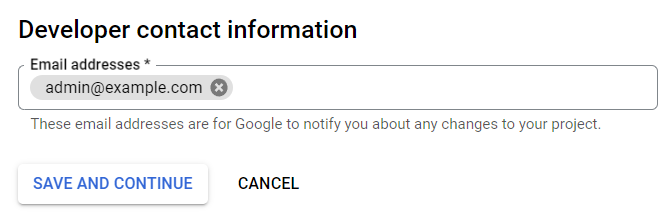
Add the scopes
email,profile,openid(don't forget to click "Update")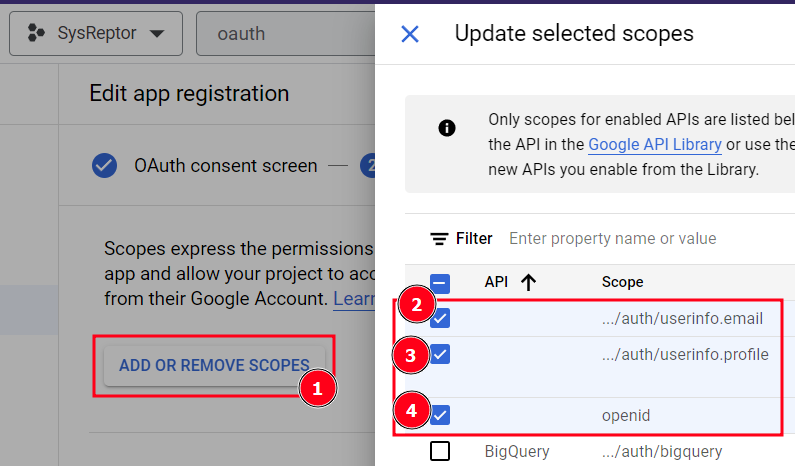
-
Click "Save and Continue" and verify your data
-
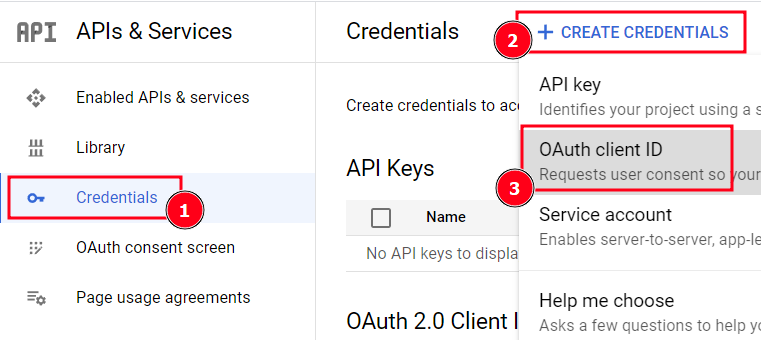
Go to "Credentials", "Create Credentials" and select "OAuth client ID"
-
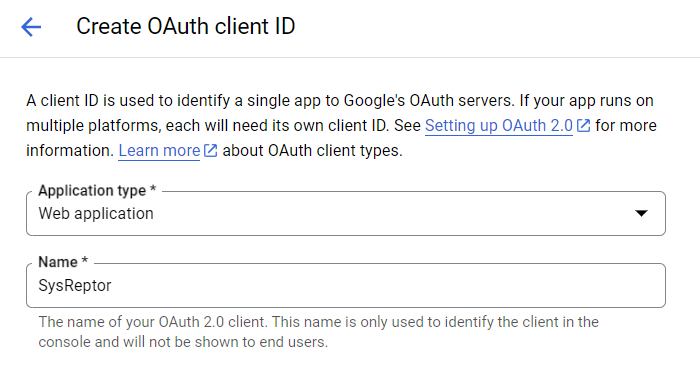
Select "Web Application" at "Application type" and enter a name
-
You don't need any JavaScript origins
-
Enter the URL to your SysReptor installation with the path
/login/oidc/google/callbackas Authorized redirect URI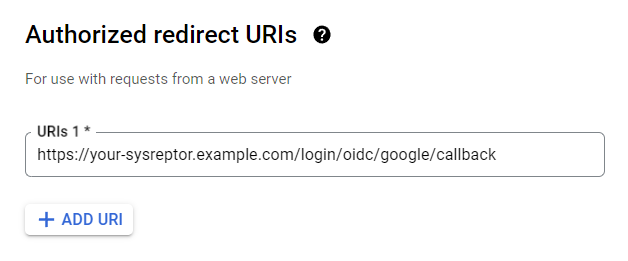
-
Click "Create"
You should now have the following values:
- Client ID
- Client secret
SysReptor Configuration
Create your OIDC configuration for SysReptor...
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 | |
...and add it to your application settings (OIDC_AUTHLIB_OAUTH_CLIENTS).
The OIDC client needs to be able to establish a network connection to Google. Make sure to not block outgoing traffic.
Other JSON fields, user_identifier_claim, and general SSO limitations are covered in Generic OIDC configuration and Limitations.
Limitation: Reauthentication
SysReptor reauthenticates users before critical actions. It therefore requires users to enter their authentication details (e.g. password and second factor, if configured).
Google does not support enforced reauthentication. The reauthentication therefore redirects to Google. If the users are still authenticated at Google, they are redirected back and SysReptor regards the reauthentication as successful.
This is a limitation by Google.
To enforce reauthentication, users can set a password for their local SysReptor user. This will enforce reauthentication with the local user's credentials.
Edit / View on GitHub